Strengthen your team. Reduce cyber risks. Free up time.
Train your employees on IT security and the GDPR - strengthen your IT security
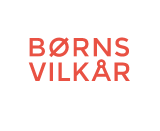
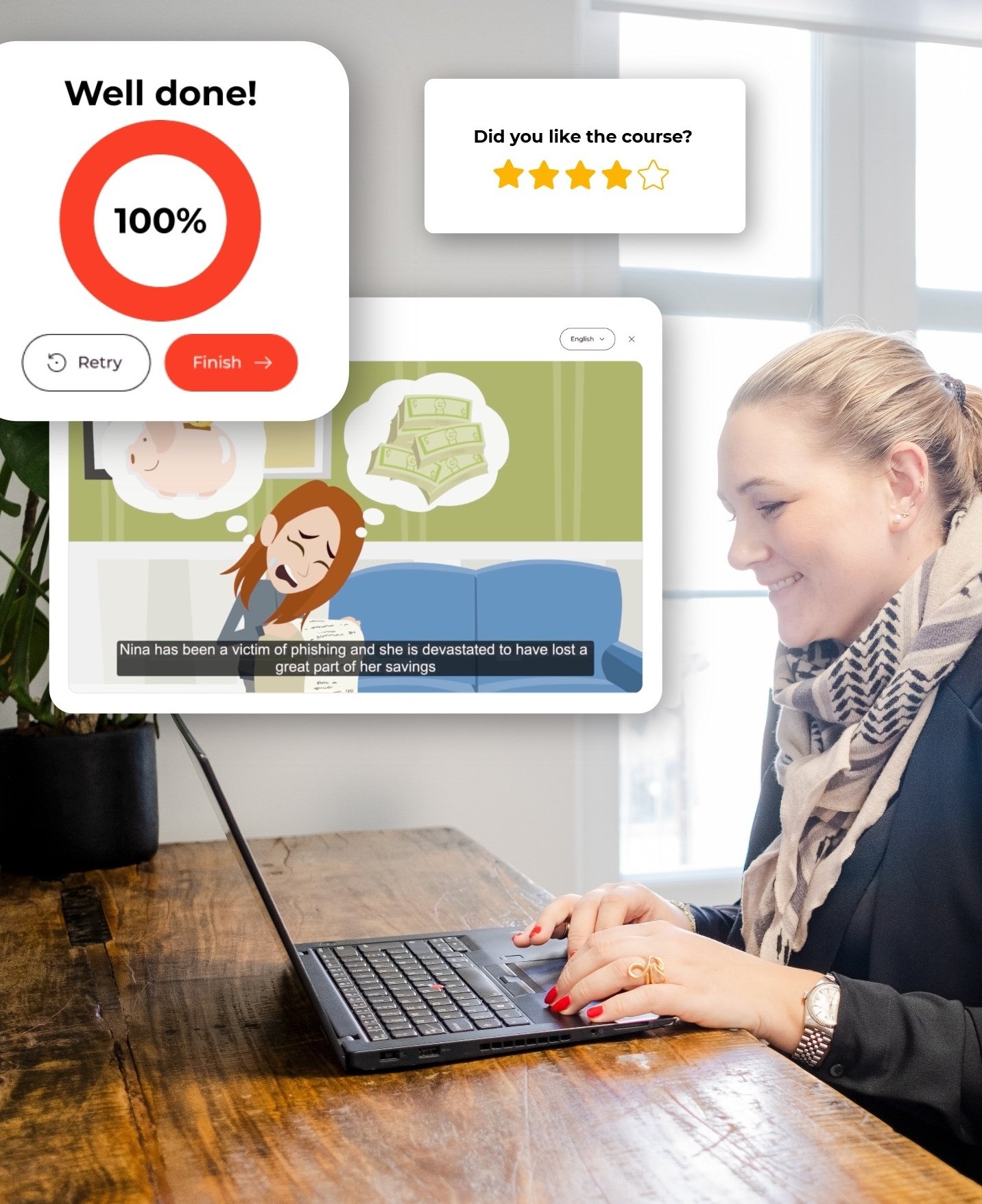
We offer simple, continuous training and interactive courses that actively change behavior to strengthen your IT security culture, rather than just checking a box.
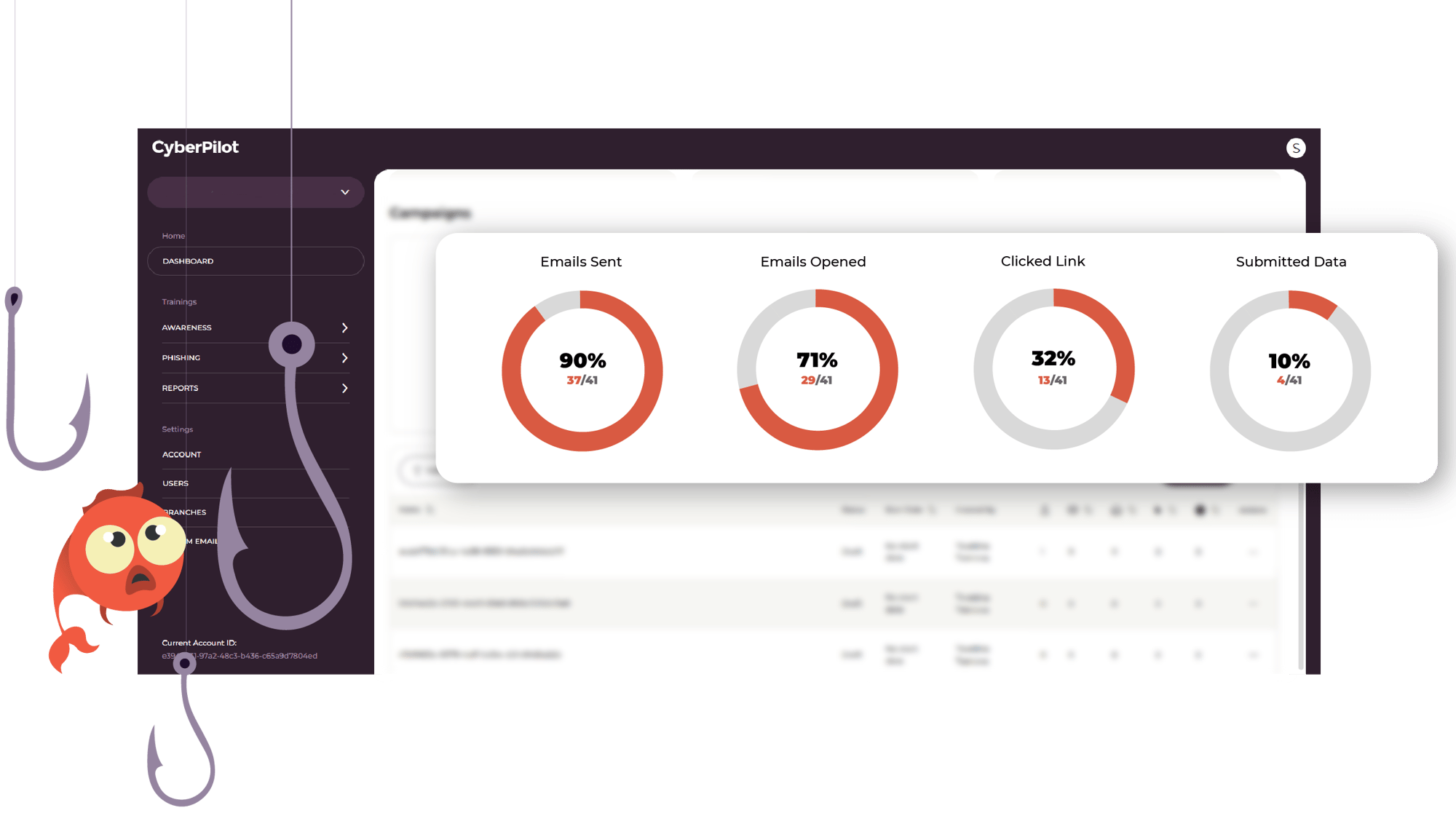
Train your employees to recognise phishing in their
own inbox
With our realistic simulations, your employees can practice recognising suspicious emails and improve their ability to detect phishing attempts. With our easy-to-use reporting, you can effortlessly track progress.
Do you find that employees ignore security training or fall for phishing simulations?
Uncover employee attitudes and perceptions about your organisation's security culture through simple questionnaires.

Why should you choose CyberPilot?
We understand that cyber security success depends on both technology and human behavior. We offer services that help organisations build robust cyber security - and we make it simple, easy and effective.
We make cyber security easy and accessible, no matter the size of your business. Our solutions are designed to be simple, effective and usable by everyone - regardless of IT skills.
From day one, we provide guidance and the tools you need to get the most out of our cyber security solutions.
You will be in
great company
The platform is easy to understand and accessible for all, no matter your skill level.
CyberPilot provides us IT security courses in a bright variety.
The employees are much more aware now, and know what to look for.
We are experiencing that users now share much more information on how they have uncovered and rejected phishing emails, with a reference to the 'set of reminders' that are presented in the CyberPilot courses.
The courses meet 100% of our expectations for the training.
I think I can see a lot of feedback from our users.
They feel more comfortable because it's now a part of their daily lives.
It's not an unfamiliar thing where they fear getting fired for clicking on a link or facing criticism from their boss. It has become commonplace that IT security is a part of our daily work.
Posters can create awareness in your organisation
Download our free posters and hang them on your walls. They will be a reminder of good habits and practices.
Templates that can help you manage your security efforts
We have several free templates on our platform and you can get them for free! They can help you create a strong cyber security culture.
Download our free E-book
Turn your team into your strongest defence with 4 simple steps and concrete tips on how to achieve compliance.

You will receive inspiration, tools and stories about good cyber security practices directly in your inbox.